A
Pengertian hardening host
Pengertian hardening host
Host Hardening adalah Prosedur yang meminimalkan ancaman yang datang dengan mengatur konfigurasi dan menonaktifkan aplikasi dan layanan yang tidak diperlukan. Contoh dari Host Hardening yaitu Instalasi firewall, instalasi antivirus, menghapus cookie, membuat password , menghapus program yang tidak diperlukan. Tujuan dari Host Hardening adalah untuk menghilangkan resiko ancaman yang bisa terjadi pada komputer.
B. Elemen Host Hardening
1. Hardening System: Security Policy (Keamanan Berdasarkan Penggunaannya)
2. Hardening System: Kriptografi (Menyimpan Suatu Pesan Secara Aman)
3. Hardening System: Firewall
4. Hardening System: IDS (Mendeteksi Jenis Serangan dan melakukan Blokade)
5. Hardening System: Backup
6. Hardening System: Auditing System
7. Hardening System: Digital Forensik dan Penanganan Pasca Insiden
Ada 2 Sumber tentang Host Hardening , Dibawah ini adalah Elemen Host Hardening yang dikutip dari Brainly
Elemen Host Hardening :
1. Physical security (Keamanan fisik)
2. Secure installation and configuration (Instalasi aman dan konfigurasi)
3. Fix known vulnerabilities (Memperbaiki kerentanan dikenal)
4.Turn off unnecessary services (applications) (Matikan layanan yang tidak perlu (aplikasi))
5. Harden all remaining applications (Harden semua aplikasi yang tersisa)
C. Langkah Host Hardening
1. Create a non-root user
Restart service dengan perintah sysctl –p
 |
| Topologi jaringan yang di pakai |
1. Create a non-root user
# adduser {username}
# passwd {username}
2.
Add non-root to the
sudoers group
# visudo
add the following line directly after the
line containing root ALL=(ALL:ALL) ALL{username}ALL=(ALL)ALL
then save and quit
3.
Add public ssh key to
non-root user
Generate key
$ ssh-keygen
4.
Deny all inbound traffic
with ufw firewall
5.
Open required ports
within the ufw firewal
6.
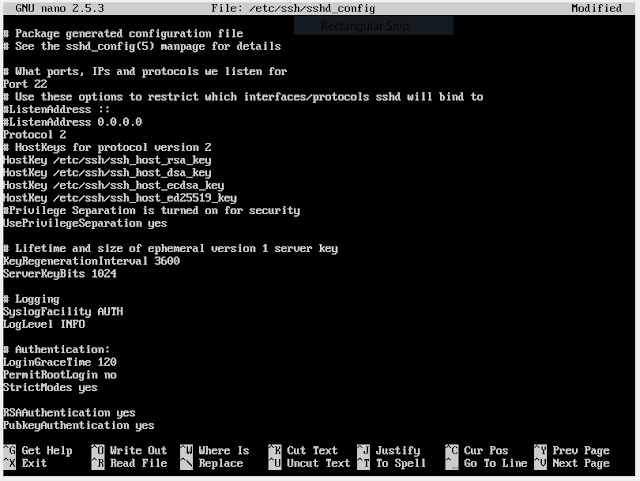
Update SSH config -
Password-less logins
ssh-copy-id {username}@{remotePublicIPAddress}
7.
Update SSH
config - Disable root login
PermitRootLogin – This flag
enables (yes) or disable (no) root login via SSH
sudo vi /etc/ssh/sshd_config
PermitRootLogin yes >
PermitRootLogin no
8.
Update SSH config -
Change ssh port
Port XX —
This is the port on which the SSH daemon listens (port 22 by default).
sudo nano/etc/ssh/sshd_config
Port 22 > Port 9001
if not change, it's not problem.
9.
Unattended upgrades
10.
Postfix for emails
11.
Logswatch to send daily summary emails
12.
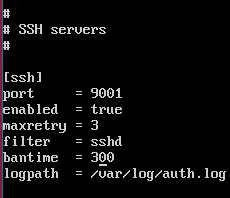
Fail2ban
Copy 2 file
Configuration file2ban
banned after failed login. Configuration do on jail.local
13.
Set the timezone to UTC and install NTP
#timedatectl
set-timezone UTC
Setting timezone menjadi UTC
#apt-get
install ntp
#timedatectl
set-ntp on
Untuk
mengaktifkan sinkronisasi dengan ntp
14.
Secure shared memory
#nano /etc/fstab
Tambahkan none
/run/shm tmpfs rw,noexec,nosuid,nodev 0 0
15.
Add a security login banner
#nano
/etc/pam.d/sshd
Comment
2 baris berikut
Buka /etc/ssh/sshd_config dan Comment baris berikut Banner
/etc/issue.net
#sudo service ssh restart
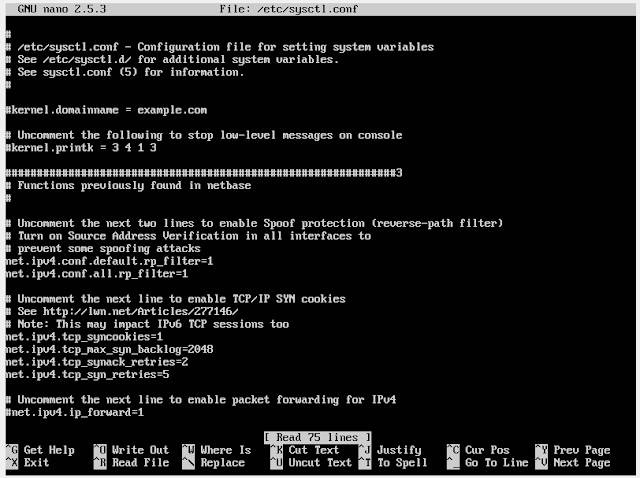
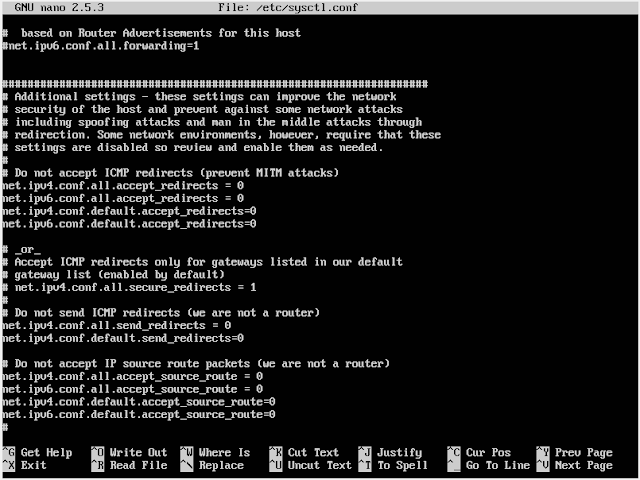
16.
Harden the networking layer
#nano
/etc/sysctl.conf
Tambahkan
dan uncomment beberapa baris seperti dibawah :
#
IP Spoofing protection
net.ipv4.conf.all.rp_filter
= 1
net.ipv4.conf.default.rp_filter
= 1
#
Ignore ICMP broadcast requests
net.ipv4.icmp_echo_ignore_broadcasts
= 1
#
Disable source packet routing
net.ipv4.conf.all.accept_source_route
= 0
net.ipv6.conf.all.accept_source_route
= 0
net.ipv4.conf.default.accept_source_route
= 0
net.ipv6.conf.default.accept_source_route
= 0
#
Ignore send redirects
net.ipv4.conf.all.send_redirects
= 0
net.ipv4.conf.default.send_redirects
= 0
#
Block SYN attacks
net.ipv4.tcp_syncookies
= 1
net.ipv4.tcp_max_syn_backlog
= 2048
net.ipv4.tcp_synack_retries
= 2
net.ipv4.tcp_syn_retries
= 5
#
Log Martians
net.ipv4.conf.all.log_martians
= 1
net.ipv4.icmp_ignore_bogus_error_responses
= 1
#
Ignore ICMP redirects
net.ipv4.conf.all.accept_redirects
= 0
net.ipv6.conf.all.accept_redirects
= 0
net.ipv4.conf.default.accept_redirects
= 0
net.ipv6.conf.default.accept_redirects
= 0
#
Ignore Directed pings
net.ipv4.icmp_echo_ignore_all
= 1
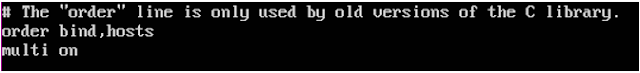
17.
Prevent IP spoofing
#nano /etc/host.conf
change like that















Komentar
Posting Komentar